
Organizations overconfident in dealing with cybersecurity incidents
New research from Immersive Labs reveals a widening gap between confidence and capability in cybersecurity.
While nearly every organization (94 percent) believes it can handle a major incident, the data tells a different story. According to Immersive’s analysis, average decision accuracy is just 22 percent, and the average containment time is 29 hours.
Google to use Android developer verification to allow safe app sideloading
Like Apple, Google has gradually made it more difficult to install apps from outside its own store. But the company is aware that neither users nor developers necessarily want to be tied to just the Play Store – this is why it has come up with the Android developer verification program.
The idea is that Google will check and verify developers so the users know they can be trusted. Now the company has an update based on early feedback it has received.

Apple Digital ID is a passport-based identity document on iPhone and Apple Watch
Apple has launched Digital ID, a new Apple Wallet-store identity document for US users that is accepted at airports and other locations.
Digital ID is created from information from a US passport, and it can be used as a travel document as well as a way of proving age. Although the company is making much of the system, it concedes that there are numerous limitations.

diVine is Vine back from the dead, thanks (in part) to Jack Dorsey
Cast your mind back a few years – well, several, actually – and you may well remember Vine. The social network focused on short-form videos, and it was killed off nearly 10 years ago. Now, re-entering a very busy social arena, Vine is back.
This time, the platform is going by the name diVine, and it is partly funded by one of Jack Dorsey’s ventures. This is not just a relaunch of the old video sharing platform; there is an attempt to resurrect as much of the original content as possible.

What do you need more -- a chief AI officer or better data? [Q&A]
According to recent research nearly half of FTSE 100 companies now have a Chief AI Officer (CAIO) -- with 42 percent of those hires made in just the past year.
Companies are clearly rushing to signal their AI credentials at board level, but is this a meaningful shift, or simply another wave of hype-led decision making? We spoke to Francisco Mateo-Sidron, SVP and head of EMEA at Cloudera, who believes that a CAIO alone can’t drive real results if enterprises don’t have data that’s built on solid foundations.
Google will now warn about battery-hungry Android apps
There are many things to consider when installing apps, particularly if there are several similar titles vying for attention. As well as things like range of features, looks and performance speed, power usage is also important to users – and Google agrees.
The company is looking to help improve the overall experience for Android users by warning about apps which can be a drain on a device’s battery. More than this, Google is working to help developers to create apps which are more power-efficient.

Modern workforce integration -- why AI agents need the same oversight as their human counterparts [Q&A]
Agentic AI is rapidly moving from concept to reality, prompting organizations globally to rethink how they integrate these technologies into their business operations. The use of AI agents in daily workflows is set to rise dramatically in the coming years, raising questions over what organizations need to do to manage them effectively, and what might happen if they fail to do so.
We spoke with Ann Maya, EMEA CTO at Boomi, about the evolution of AI agents, the steps businesses should be taking ahead of deployment, and why the principles of human workforce management may hold the key to responsible use.

Mobile threats increase ahead of holiday shopping season
New research from the Zimperium zLabs team reveals a sharp rise in mobile threats tied to the holiday shopping season.
The report shows that mishing (mobile phishing) remains the most widespread and effective mobile attack vector. Smishing messages and fake delivery alerts impersonating trusted retail and logistics brands surged up to fourfold during the 2024 holiday shopping period, with attackers using urgency-driven messages like ‘Your package is delayed, click here’ to trick users into revealing credentials or downloading malicious apps.

Rise in agentic identities leads to increased risk
The AI wave is translating into an increased number of AI agents in the workplace, which equates to a surge of both non-human identities (NHIs) and agentic identities. This is resulting in an urgent focus for CIOs and CISOs on identity threats and recovery.
New research from Rubrik Zero Labs, based on a survey by Wakefield Research of over 1,600 IT security decision makers, finds 89 percent of respondents have fully or partially incorporated AI agents into their identity infrastructure, and an additional 10 percent have plans to.

How AI is changing the role of IT leaders
Artificial intelligence has redefined what it means to lead in IT, with 63 percent of IT leaders
reporting that their roles have evolved due to advances in AI.
A study, from IT management platform Atera, finds today’s IT leaders are increasingly responsible for driving business value. 49 percent cite business value leadership -- shaping strategy and translating AI into revenue and growth – as the top area of increased importance, and 47 percent point to orchestrating human-AI collaboration as a key change in their roles.

Say goodbye to Microsoft Windows 11 and hello to Nitrux Linux 5Wi
Windows 11 remains familiar territory for many users, but it continues to frustrate those dealing with sluggish performance and high system demands on older machines. Frequent updates often fix some problems while introducing others, leaving users searching for an alternative. For those ready to move away from Windows, there's Nitrux Linux 5.
After a long wait, the latest version of the Debian-based Linux distribution has arrived, bringing with it a wealth of changes and improvements. Top of the list is the Hyprland desktop which replaces KDE Plasma.
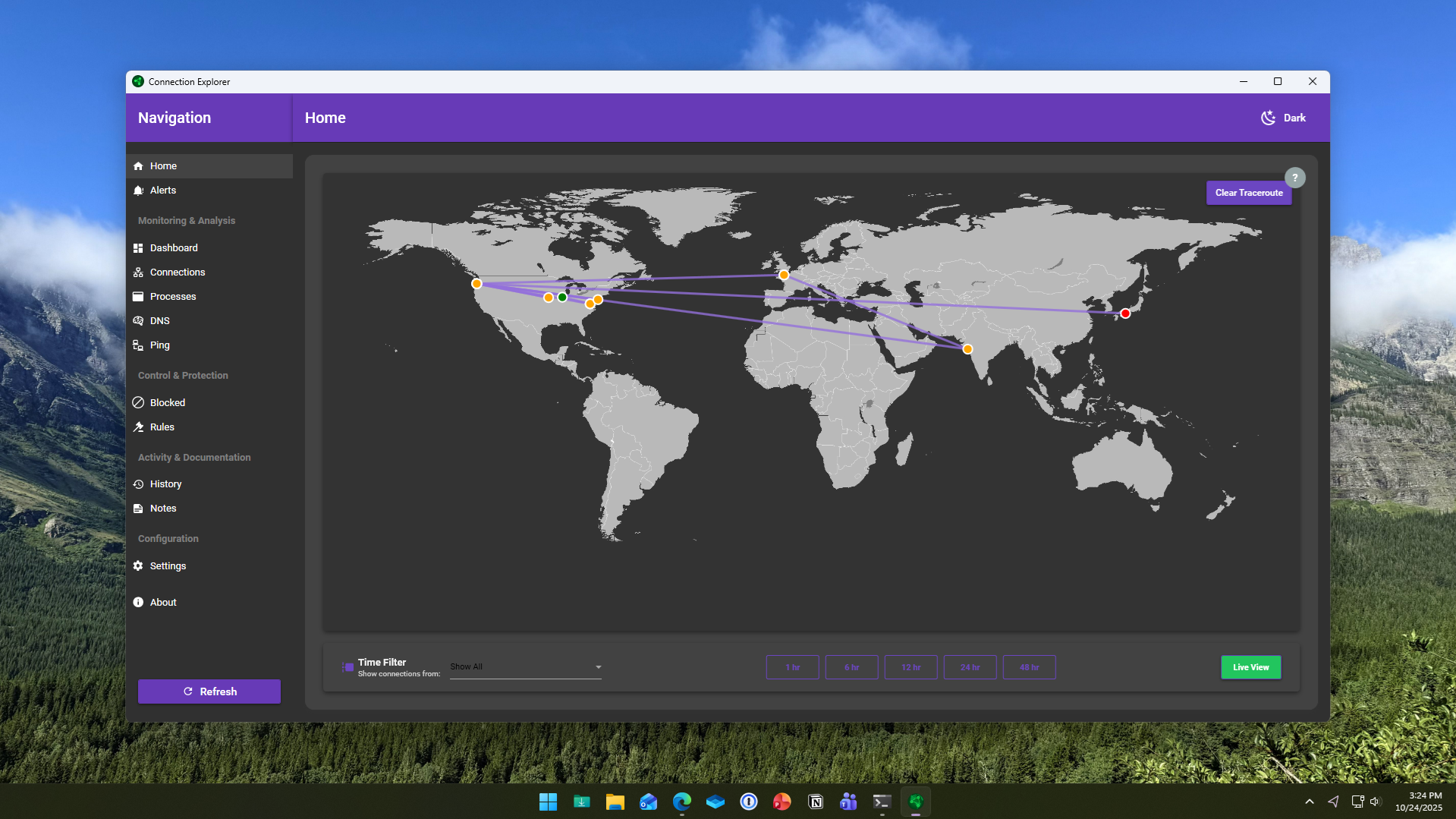
Connection Explorer shows where your PC is sending data in real time
Stardock has launched a new application for Windows called Connection Explorer, a beta tool designed to reveal and visualize every network connection made by a PC. Aimed at improving data transparency, it allows users to monitor, understand, and control how their devices communicate online.
The software maps out every connection a computer makes, transforming complex background activity into a readable visual interface. Stardock says the goal is to give users direct insight into how data flows between their systems and the internet, removing the guesswork from identifying unfamiliar or unwanted activity.

New year, new Microsoft OS -- the stunning Windows 26 is everything Windows 12 should be
Every so often, we get hints about Windows 12, but Microsoft has yet to announce it. Now that the tech giant is only officially supporting one Windows OS, perhaps that will change.
But as 2025 draws to a close, and with a new year on the horizon, it’s time to look forward to fresh beginnings and groundbreaking innovations. It’s time for a new Microsoft operating system. Let me introduce you to Windows 26.

Better cyber hygiene could have prevented 92 percent of incidents
A new report reveals that 92 percent of organizations that experienced a security incident in the past year believe stronger cyber hygiene could have prevented it, underscoring how persistent execution gaps continue to leave organizations exposed to preventable risk.
The study by Sapio Research for Swimlane shows that despite unprecedented spending on cybersecurity tools and services, foundational security practices remain inconsistent and often overlooked.

OWC expands Thunderbolt 5 range with StudioStack and Mercury Helios 5S
Other World Computing has added two new products to its Thunderbolt 5 lineup with the launch of the OWC Mercury Helios 5S and OWC StudioStack. Both devices are designed to provide professionals with faster data transfer, expanded connectivity, and flexible upgrade options across Mac and PC.
SEE ALSO: OWC's latest portable SSD offers up to 8TB in a palm-sized design
