Scientists say finding extraterrestrial life and curing all genetic diseases could both happen in the next decade
Humanity’s search for life beyond Earth took center stage at the Dubai Future Forum 2025, held on November 18 and 19, where scientists said new methods for studying distant worlds could lead to the discovery of extraterrestrial life within a decade. The event also explored advances in gene editing, AI and global demographics, offering a wide view of the forces shaping the future.
Dr. Nikku Madhusudhan, Professor of Astrophysics at the University of Cambridge, said there is a “good chance” researchers will detect life on another planet soon. He said ongoing studies of exoplanet atmospheres are revealing traces of carbon-based molecules that could point to biological activity. He added: “In my mind, the question is not whether we will find life, because there’s a good chance we will -- the question is: are we prepared to find life as we don’t know it?”

Nearly every UK company hit by supply chain attacks despite big spending
BlueVoyant has released its sixth annual State of Supply Chain Defense report, offering a detailed look at how third-party risk is handled across regions, industries, and maturity levels.
The findings show widening gaps between investment and outcomes, rising breach rates, and growing use of AI to support vendor oversight. The research surveyed one thousand eight hundred senior IT leaders across eleven countries, including three hundred from the UK, and reveals how UK organizations compare with global trends.

Tuxedo halts Linux ARM laptop project over Snapdragon X Elite issues
Tuxedo Computers has paused development of its planned Linux ARM notebook based on Qualcomm’s first-generation Snapdragon X Elite chip, bringing the eighteen-month project to a halt.
The company says the device won't now move forward in its current form due to technical limitations that prevent it from meeting the standard expected of a Linux-first laptop.

Notepad update begins rolling out to Windows Insiders
Microsoft has begun rolling out a new Notepad update to Windows Insiders in the Canary and Dev Channels. The update introduces two big additions to the Windows 11 text editor: table support, and faster streaming-style output for its AI writing tools.
The update, released as version 11.2510.6.0, expands Notepad’s lightweight formatting features while also customizing how AI responses appear.

Social media and marketplace scams surge ahead of the holiday season
New research from online protection company Malwarebytes exposes how social media and online marketplaces have become hotbeds for holiday shopping scams.
It finds that 51 percent of people encounter scams on social media weekly while an unlucky 27 percent meet scams daily. For marketplace shoppers, 36 percent are hit with a scam weekly and 15 percent experience one daily.

Security teams want automation but 96 percent face problems implementing it
A new survey of 750 senior cyber security professionals across the US, UK and Australia, carried out by Opinion Matters for ThreatQuotient, finds 97 percent now regard automation, increasingly powered by AI technologies, as essential to business operations.
However, despite 49 percent of respondents obtaining net new budget allocation for cybersecurity automation this year -- up from 39 percent last year -- 96 percent still face persistent challenges, particularly around technology limitations, lack of trust in the outcomes of automated processes, and insufficient time to implement solutions.

Why CISOs are betting on identity firewalls to stop the next breach [Q&A]
The network firewall was designed for a world that doesn’t exist anymore. When corporate assets sat behind a data center perimeter, inspecting packets between ‘inside’ and ‘outside’ made sense.
But today, with workloads spread across multiple clouds, SaaS platforms, and edge environments, that perimeter has dissolved. Attackers don’t need to smash through firewalls when they can compromise privileged credentials and operate from within. A rogue or stolen admin account can cause catastrophic damage, something no network firewall can stop. The battlefield has shifted from networks to identities.
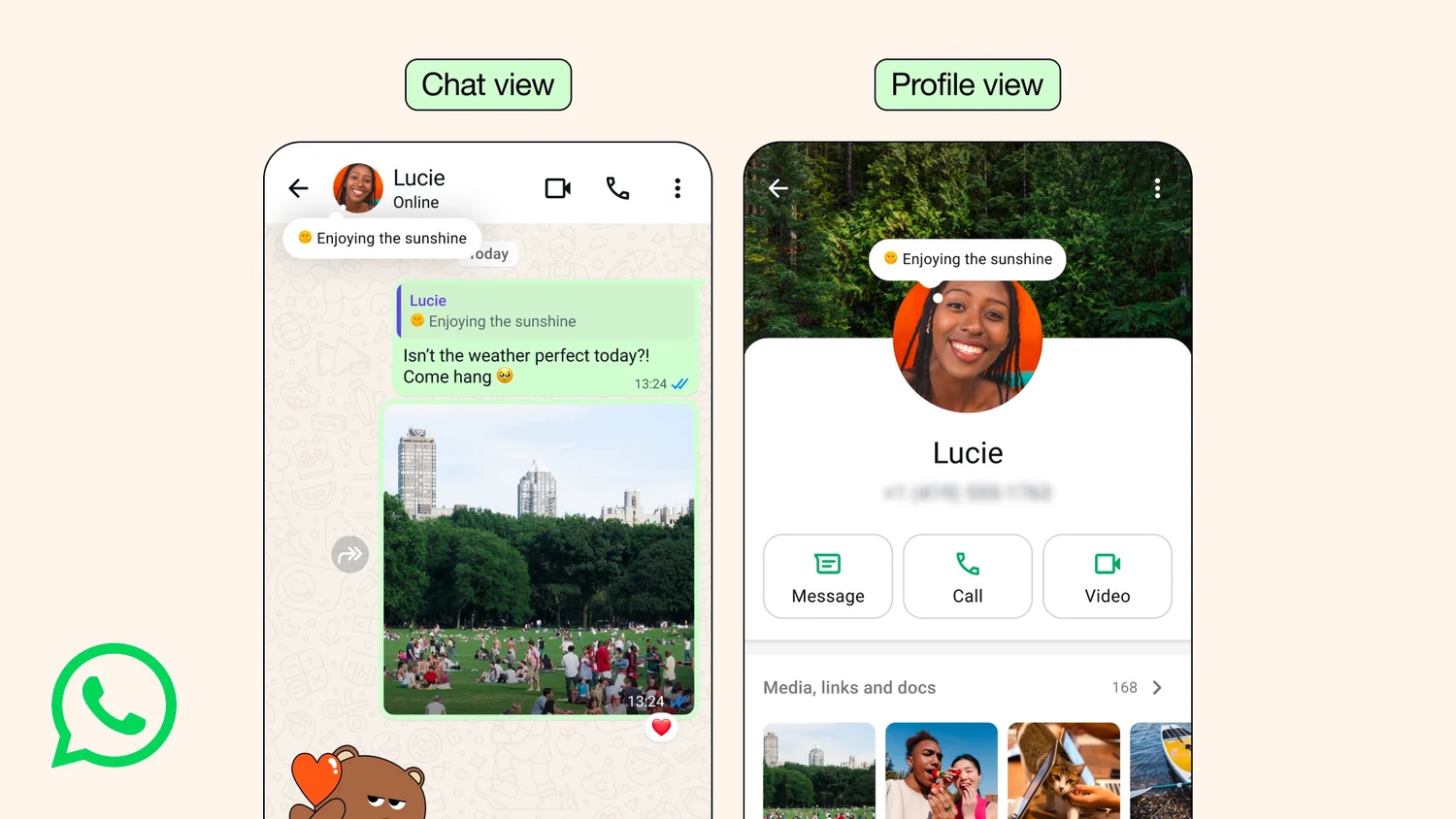
WhatsApp brings back the About feature to supplement statuses
If you are a seasoned user of WhatsApp, brace yourself for a blast from the past. The company has just announced that it is bringing back one of its earliest features in a new and improved form.
What is returning is the About feature, a simple text field that can be used to share information about yourself, your availability, or anything else you can think of. It is not entirely dissimilar to the Notes feature of Instagram.

Google updates Android Quick Share for compatibility with Apple AirDrop
Out of the blue, Google has announced a significant change to the Quick Share feature of Android. The company says that – on a limited number of devices – Quick Share can now be used to share files and photos from Android to iPhone thank to newly added compatibility with Apple’s AirDrop.
The strange and sudden interoperability comes as good news, but it is not clear how many Android devices will ultimately be able to take advantage of this change, or when. It is also not clear quite what prompted the move from Google, although the company has quite a lot to say about what is involved.
Microsoft open sources Infocom’s Zork trilogy
Microsoft, in conjunction with Activision, Team Xbox, and its Open Source Programs Office, has announced plans to open source some of Infocom’s most iconic interactive fiction. Zork I, Zork II, and Zork III will be released under the MIT License, placing the code for one of the most recognisable early computer game series into accessible public repositories. As someone who spent many hours playing the Zork trilogy (and other Infocom games) over the years, this is fantastic news.
Developers, students, and researchers will be able to examine the structure of the original titles directly rather than relying on secondary documentation or archived binaries. It will also provide a clearer view of how Infocom’s early work was built, maintained, and adapted across platforms.

IBM and Cisco announce partnership to create a distributed network of fault-tolerant quantum computers
IBM and Cisco have announced plans to work together on a connected network of large-scale, fault-tolerant quantum computers. The collaboration will unite IBM’s progress in quantum hardware with Cisco’s research into quantum networking, creating a system designed to link together multiple advanced quantum machines.
The companies expect this direction to expand quantum computing beyond the limits of individual systems, supported by a planned demonstration of networked quantum computers within five years and further work towards distributed quantum computing in the early 2030s.

Logitech opens its first U.S. experience store in San Francisco, with a giant MX Master 4 mouse
Logitech is preparing to open a pop-up store in San Francisco’s Union Square, giving visitors access to its latest products and a closer look at its MX line. The walk-in hub will remain open until late December.
A preview session for media and creators is planned for the first afternoon, offering early access to the layout and product stations. The store will allow Logitech to show how its MX products fit into creative and productivity workflows, and the MX Master 4 mouse is placed at the center of the experience --literally. There will be a giant version of it there for people have photographs taken with.

One in 11 new Black Friday websites is malicious
Retailers aren’t the only ones to want to make the most of Black Friday, it’s a boom time for scammers too. New analysis by Check Point reveals that one in 11 newly registered Black Friday-themed domains is classified as harmful.
October saw 158 new Black Friday related domains, a 93 percent increase over the 2025 monthly average. Early November intensified that growth, with more than 330 new related domains appearing in only the first 10 days.

Over 71 percent of in-house IT builds fail to deliver
A survey of over 2,000 IT and security decision-makers finds that 71 percent of in-house IT builds are eventually abandoned. In heavily regulated industries like manufacturing and finance this rises to 83 percent, which underscores how complexity and compliance pressures make homegrown systems difficult to sustain.
The study from Exclaimer calls this ‘The DIY Mirage’, a false sense of control and efficiency that fades as maintenance demands, compliance risks, and long-term costs grow.
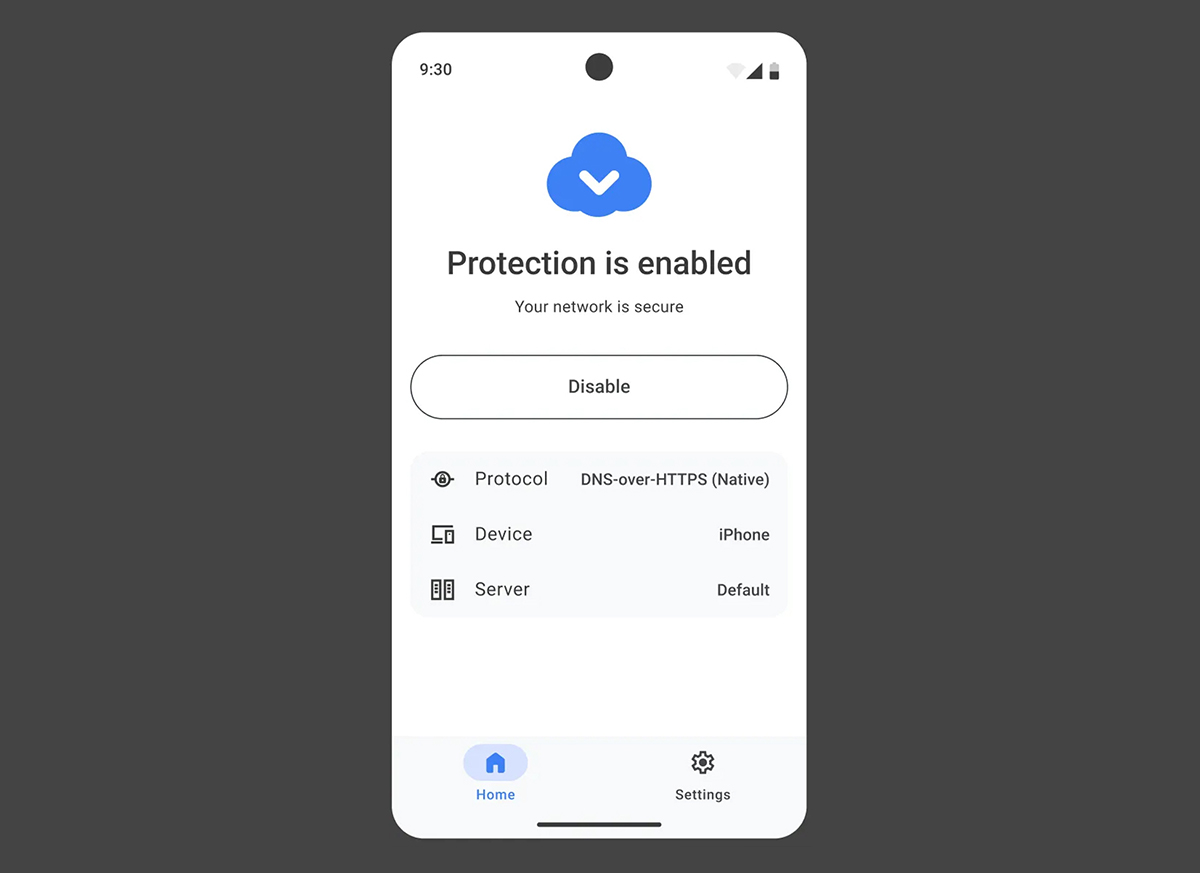
AdGuard launched AdGuard DNS, a lightweight DNS app for Android and iOS
AdGuard has released a mobile app for DNS-level protection on iOS and Android, offering a simple way to block ads, trackers and harmful sites via encrypted DNS. AdGuard DNS targets users who want network-level filtering while avoiding the complexity of full ad-blocking or VPN tools.
The app is easy to set up and use. After installing it, users can link a device to their AdGuard DNS account by entering a Setup ID from the dashboard or by scanning a QR code.