Hackers are exploiting critical WinRAR bug exposed last month
Towards the end of last month, security researchers revealed details of a critical bug in that stalwart of the compression world, WinRAR. The bug is many years old and although it relates to the rarely-used ACE format and has since been patched, it has been discovered hackers are actively exploiting it since it was made public.
The 19-year-old bug in the file UNACEV2.DLL (CVE-2018-20250) allows for an attacker to execute malicious files hidden in compressed archives. Over 100 exploits have been found that take advantage of people who are yet to update to a secure version of the software... and that number is growing. McAfee reports attackers using Ariana Grande's album "Thank U, Next" as a lure to encourage victims to extract dangerous archives, but other security researchers report the use of images.

Gearbest issues response to data breach
Following on from yesterday's story about eCommerce site Gearbest leaking customer data the company has issued an official response to ethical hacker Noam Rotem’s report.
It says that its own servers are secure but that, "external tools we use to temporarily store data" may have been accessed by others leading to security having been compromised.

A fifth of Americans don't trust anyone to protect their data
Around 20 percent of Americans suffer from security fatigue and don’t trust anyone to protect their personal data according to a new study.
The research from hardware security company nCipher Security reveals that many people want more control over their personal data privacy and most want tighter controls on how others handle and safeguard their personal data.
Gearbest security flaw leaks millions of order and user details
A badly configured server at Gearbest, the Chinese purveyor of technology and other stuff online, has leaked millions of user profiles and order details.
White hat hacker Noam Rotem discovered an Elasticsearch server that was -- indeed still is at the time of writing -- leaking millions of records each week. These include customer data, orders, and payment records. The server wasn't protected with a password, potentially allowing anyone to search its data.

Businesses plan to use more AI and machine learning in cybersecurity this year -- even though they don't understand it
The use of more artificial intelligence to improve security has been touted for a while. New research from Webroot reveals that a majority of business are now actively exploring the technology.
It finds 71 percent of businesses surveyed in the United States plan to use more artificial intelligence and machine learning in their cybersecurity tools this year. However, a worrying 58 percent say that aren't sure what that technology really does.

Analysis of Remote Access Trojans helps understand third-party business risk
Remote Access Trojans (RATs) are often used to steal information from enterprise networks. By looking at network metadata, analysts at threat intelligence firm Recorded Future have been able to identify RAT command-and-control (C2) servers, and more crucially, which corporate networks are communicating to those controllers.
This offers insight about third-party organizations that Recorded Future clients can use to get a better understanding of potential third-party risk to their own data.

Brits are more scared of spiders than cybercrime
Cybercrime and hacking has overtaken flying, dogs and clowns in the top 10 list of things the British are most scared of, but still only ranks in sixth place behind spiders, heights, snakes, dentists and small spaces.
Arachnids top the list despite there being less than a one-in-a-million chance of being bitten by a spider badly enough to warrant going to hospital in the UK.
Stricter payment requirements in Europe could drive fraud elsewhere
From September this year the second Payment Services Directive (PSD2) comes into force across the EU. This will require payment service providers to offer strong customer authentication (SCA) and third-party access to bank accounts or risk losing their their payment provider license.
But a new report today from fraud prevention company iovation suggests that stricter requirements for fraud prevention in Europe will drive fraud to other regions such as the US.

Researchers find two Android malware campaigns with over 250 million downloads
Check Point Research has uncovered two massive mobile adware and data stealing campaigns, which have already had a combined total of over 250 million downloads globally.
Both target mobiles using Android, and exploit the mobile app development supply chain to infect devices and perform malicious actions.

Two-thirds of Android antivirus apps block less than 30 percent of threats
In one of the biggest tests of Android antivirus software ever conducted, out of 250 apps tested the majority proved to be dubious, unsafe or ineffective.
Independent testing organization AV-Comparatives put the apps to the test against an array of common threats and found that some are not properly protecting users.
Microsoft to start selling Windows 7 Extended Security Updates from April 1
While Windows 10 enjoys a significant and growing userbase, there are still many Windows 7 users out there. This includes a large number of enterprise users, and for these customers security is of paramount importance.
Last month we learned about the pricing for Windows 7 Extended Security Updates (ESU) which will be available when support for the aging operating system ends in 2020. Now we know that ESU will go on sale from the beginning of next month.
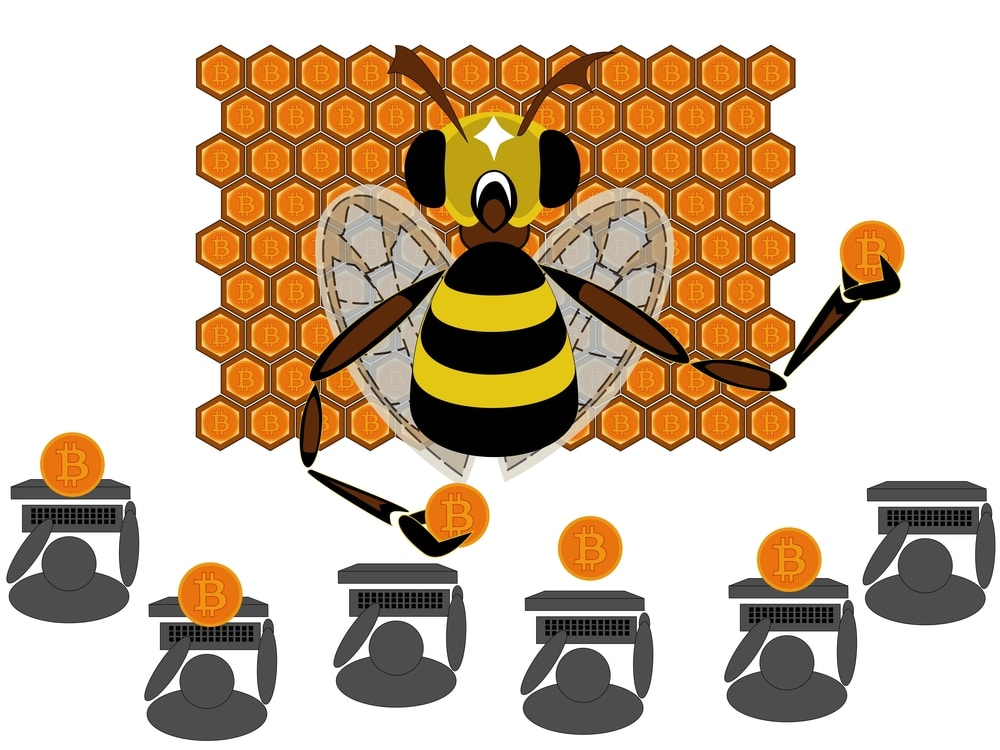
Coinhive dominates malware charts before being shut down
Coinhive continued to hold the top spot in Check Point Research's February Global Threat Index, impacting 10 percent of organizations worldwide, even though its services were shut down on March 8th.
In February, the two most prevalent malware variants were cryptominers, followed by the Emotet banking Trojan. Coinhive has seen a downward trend in its global impact, from 18 percent of organizations in October 2018 to 12 percent in January 2019 and with a further two percent drop in February.

Secure BYOD, the BYOD way
Bring your own device (whereby employees work from personal devices like their mobile phones) is quickly becoming the norm in today’s business environment. Companies that embrace BYOD are able to give employees more freedom to work remotely, resulting in increased productivity, cost savings and talent retention. In fact, 85 percent of organizations now allow BYOD for at least some of their stakeholders, including employees, contractors, partners, customers and suppliers.
It is important to note that BYOD does change an organization’s threat landscape and requires security tools that are different than those that are used to protect managed devices. Unfortunately, a widespread misunderstanding about this point has contributed to an unfounded assumption that BYOD is inherently riskier than the traditional way of doing things. In reality, this is a myth fueled by companies that fail to implement proper security tools and processes for protecting data in BYOD environments. Consider the following findings from a recent report on BYOD and security:

Google recommends upgrading to Windows 10 to avoid unpatched Windows 7 zero-day that's being actively exploited
Google is warning users of Windows 7 that they are at risk from a privilege escalation zero-day bug -- and the advice is to upgrade to Windows 10 as there is no patch currently available for the actively exploited vulnerability.
The problem stems from two vulnerabilities being exploited in combination -- one in Chrome, and one in Windows. Having pushed out a patch to its Chrome web browser, Google is warning that Windows 7 users are still exposed until such a time as Microsoft develops a patch.

Banking Trojan attacks up by 16 percent in 2018
Attacks using banking Trojans are among the most popular with cybercriminals as they are focused directly on financial gain.
According to a new report from Kaspersky Lab, 889,452 users of Kaspersky Lab solutions were attacked by banking Trojans last year, an increase of 15.9 percent compared to 2017.
