
Apple Music time-synced lyrics now available on Samsung smart televisions
There are many music streaming services these days, such as Spotify, Tidal, and YouTube Music. My favorite, however, is Apple Music. Why? Well, besides the excellent mobile interface, it has a very large library of music. Not to mention, the human-curated playlists are second to none. Plus, Apple Music finally has a web player now -- a much desired feature.
Another cool aspect of Apple Music is time-synced lyrics. When you are listening to some songs (not all), you can have the lyrics display on your device's screen -- timed to the music. It works great, and it is even an option on Apple TV, enabling you to have a karaoke-like sing-along with friends and family. Apple Music is no longer just an Apple-only affair though, as it is available on Android devices and some smart televisions too. Today, Samsung announces that the aforementioned Apple Music time-synced lyrics feature is finally available on its smart TVs.

MAINGEAR TURBO is an impossibly small AMD Ryzen 3000XT gaming desktop
If you want a proper gaming PC, you need a full ATX motherboard and a massive tower full of fans, right? Actually, no. Nowadays, there are very capable mini ITX and micro ATX motherboards, making it possible to have a lot of power in a small package.
But holy cow, I never expected to see this much power crammed into such a small space! Today, MAINGEAR launches the TURBO -- a beautiful and impossibly small AMD Ryzen 3000XT gaming desktop. Just how small is it? A very impressive 7" x 14.4" x 12.3". This diminutive liquid-cooled beast can be configured with a processor ranging from the AMD Ryzen 5 3600 to the 3950X -- including the new 3000XT chips. You can choose up to 16TB of storage and up to 64GB of RAM. Graphics cards from both NVIDIA and AMD are available.

Debunking four object storage myths
There is no arguing the fact that data continues to grow at an exponential rate, particularly unstructured data, which is predicted to represent 80 percent of all data by 2025. And because of trends likes IoT, the continued proliferation of mobile devices and the rise of remote work, this growing data is being used and accessed in new ways.
At the same time, it’s become increasingly clear that traditional SAN and NAS storage technologies cannot scale to meet these data growth demands nor support the need for data to be readily accessible from anywhere and at any time. To ensure these surging volumes of data are accessible and manageable, more and more enterprises are turning to object storage to meet their storage needs. However, there are still several misconceptions that persist about object storage. Here are four myths about the technology debunked.

How to avoid common cloud migration challenges
Most IT architectures are complicated. If you’re considering migrating to the cloud, you’re right to be concerned about the many changes that will be required of your architecture and your organization as you make your transition. Cloud migration challenges continue to give organizations anxiety, even though the cloud has been around for nearly 20 years.
Of course, nobody embarks upon a cloud migration expecting to fail. The basic problem is that few people understand the hidden challenges of such a complex project, particularly as it relates to ongoing processes and operations. Unexpected challenges are the curse of any major undertaking, and cloud migrations are truly full of unexpected challenges.

How COVID-19 changed the future of work
COVID-19 forced businesses across the globe to rapidly adopt remote work in order to adhere to social distancing and stay-at-home orders. For some companies, this transition was seamless, especially those that already implemented cloud and the necessary supporting tools within their organizations. Others struggled to adapt their workforces to this highly remote, cloud-first environment. In fact, 41 percent of enterprises have not taken any steps to secure access for their remote workers despite the fact that 65 percent enable personal devices to access managed applications.
To quickly support remote work, organizations were spurred to adopt cloud and allow employees to access the corporate network from unmanaged devices. However, cloud and BYOD environments call for specific security solutions, and organizations that failed to simultaneously implement the necessary controls also expose themselves to more risks, including insider threats. Even once stay-at-home orders are lifted and some businesses choose to return to the workplace, COVID-19 had such an impact on the way we work, making it likely that the following post-pandemic predictions may occur.
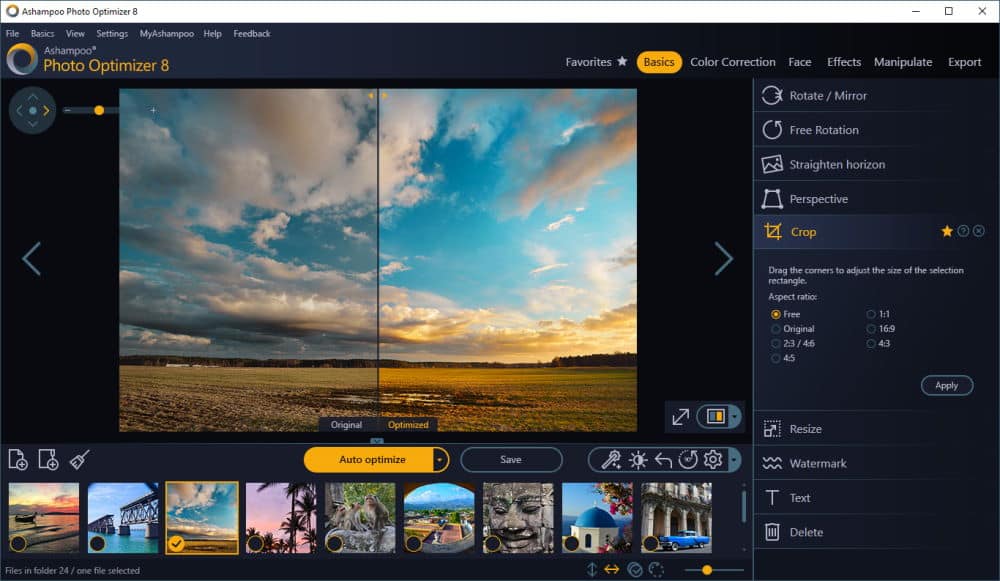
Ashampoo Photo Optimizer 8 promises much-improved 1-click photo fix
German software developer Ashampoo has unveiled Photo Optimizer 8.0, a major new release of its Windows photo-editing tool. The first major update since June 2018, version 8 builds further on the 1-click optimization tool introduced in version 7, plus offers additional manual fine-tuning tools alongside a new perspective correction feature.
Photo Optimizer 8 opens with what Ashampoo admits is a 'significantly improved' 1-click correction tool, designed to detect potential weaknesses in the original photo and provide improvements with no user involvement required. The improved algorithm has undergone two years of development and trial runs, with many thousands of setting combinations tested to help lift photos suffering from dull colors, poor lighting and a lack of contrast.
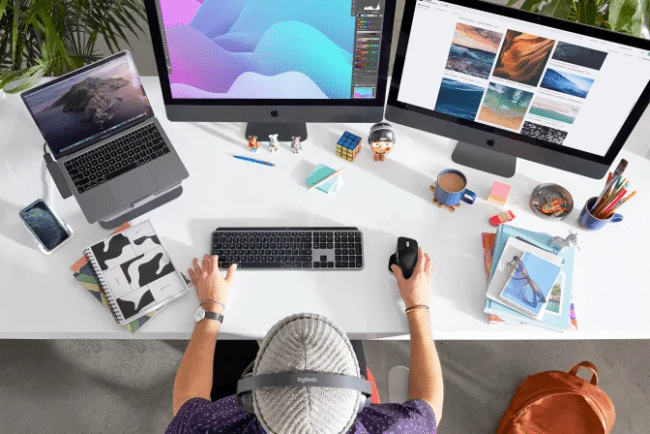
Logitech launches Apple-focused variants of MX Master 3 and MX Keys
Want to know a little-discussed fact about Apple? Despite the company's historic excellence in design, it has never created a good mouse. It's true! Throughout the company's entire history, including today, all Apple mice have been terrible. With that said, its trackpads are absolutely brilliant, and they are still a class-leader. No Windows laptop has a better trackpad than a Mac.
If you like Mac computers but hate Apple mice, there is one excellent solution -- buy a third party mouse. You can never go wrong with a Logitech mouse, and today, the company launches an Apple variant of its popular MX Master 3. In addition, Logitech is launching two Apple-focused keyboards as well -- a Mac-optimized version of the MX Keys and the K380 for Mac Multi-Device Bluetooth Keyboard.

How to uninstall Microsoft Edge from Windows
Microsoft has been quite aggressive in pushing out the Chromium-based version of Edge, and not everyone is happy about it.
There is understandable anger at having a browser that isn't necessarily wanted being forcibly installed -- and to add insult to injury, Microsoft has also made it impossible to uninstall Edge. But there is actually a way to get rid of the browser. Here's what you need to know.

Linux users might find themselves paying money to use LibreOffice one day
If you are a Linux nerd or Windows user without much money, you probably use LibreOffice. That free software is actually quite good, although Microsoft's Office is far superior. Regardless of how you feel about the Windows-maker, its office suite of software is second to none. If you use Windows or Mac and can afford it, I always recommend using "real" Word and Excel over knockoffs, such as the aforementioned LibreOffice's Writer or Calc. Sadly, other than the web version, Microsoft Office is not available for Linux. With that said, as a Linux user, I appreciate LibreOffice's existence and use it regularly.
But what if LibreOffice wasn't free? Would people still use it if it cost money? Some folks became very worried about that exactly, as the release candidate of LibreOffice 7.0 labeled itself as "Personal Edition." To some, it was a sign that a paid version of LibreOffice was on the horizon. Well, guess what? They weren't totally wrong. In the future, you might find yourself paying money to use LibreOffice software. According to a new blog post from The Document Foundation Board aimed at quelling fears, however, there is no need to panic.

How pre-installed adware can cause trouble for mobile users
New analysis carried out by Kaspersky of attacks on mobile devices has revealed that 14.8 percent of its users who were targeted by malware or adware in 2019 suffered a system partition infection, making the malicious files undeletable.
It also finds that pre-installed default applications have role to play, depending on the brand, the risk of applications that can't be deleted varies from one to five percent in low-cost devices and goes up to 27 percent in extreme cases.
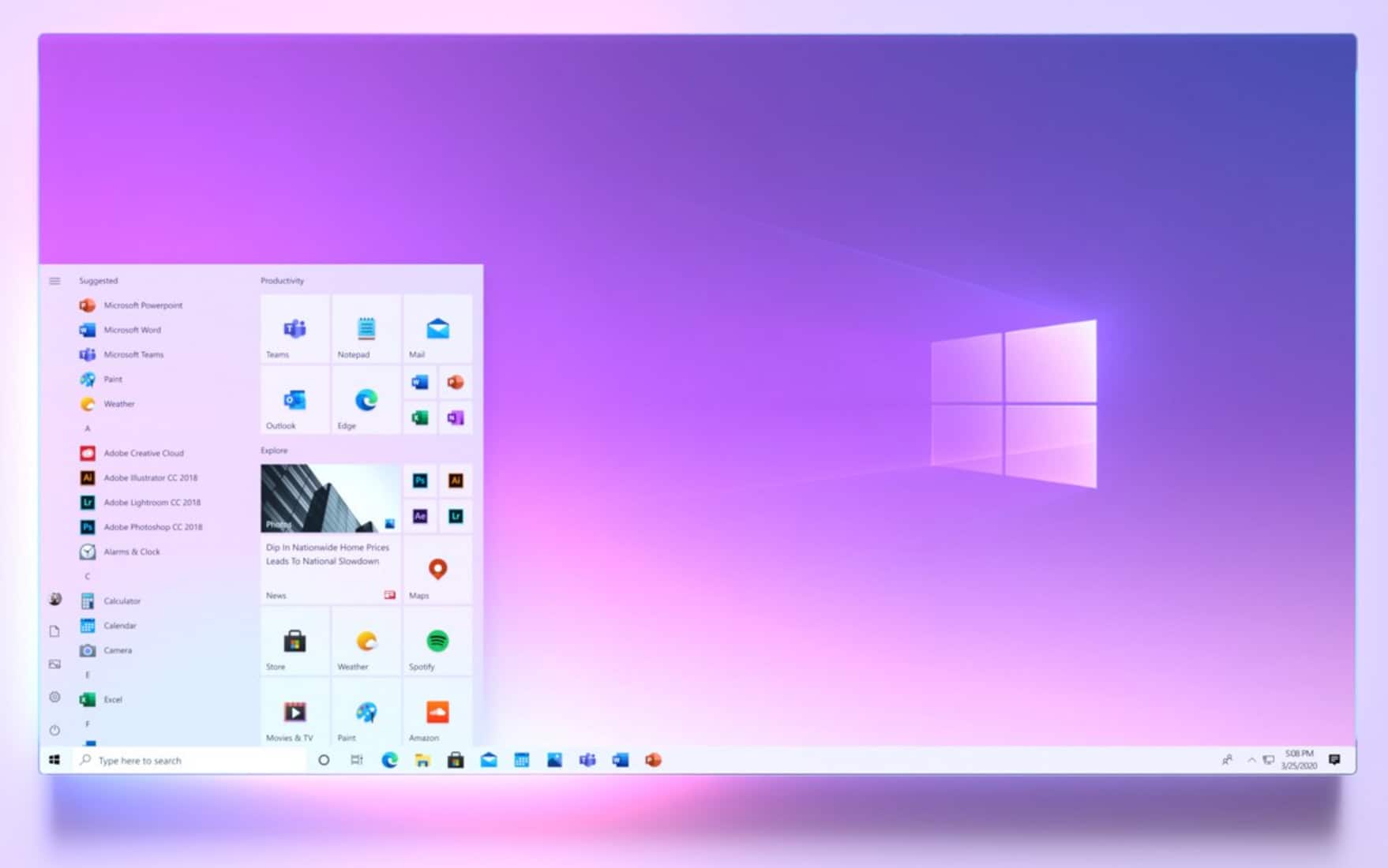
How to enable the new Start menu in Windows 10
After giving us a tease of a redesign, Microsoft rolled out the new look Start menu in Windows 10 build 20161.
But while there was a great deal of excitement about the cleaner, more refined look complete with translucent backgrounds, many Windows users were disappointed to find that the new Start menu was not available to everyone. Here's what you need to do to see the new Start menu.
Microsoft blocks users from upgrading to Windows 10 May 2020 Update because their PC settings aren't supported
We've already seen Windows 10 May 2020 Update causing a range of problems for users, including login issues, problems with Storage Spaces and issues with OneDrive. But there are also some people for whom even the installation is problematic.
We've already heard about people being unable to get the update because their "device isn't quite ready". Now there are reports that some users are seeing a message informing them that "this PC can't be upgraded to Windows 10". In the error message, Microsoft tells affected users that: "Your PC settings aren't supported yet on this version of Windows 10".

HyperX launches Alloy Elite 2 mechanical gaming keyboard with pudding keycaps
If you are a serious PC gamer, I hope you own a mechanical keyboard. Whether gaming on a laptop or desktop, you should absolutely have a high-quality mechanical keyboard and mouse plugged in. After all, there is a good chance your competition is using these things, so why should you be at a disadvantage?
If you are in the market for a mechanical keyboard, I have good news. Kingston's gaming division, HyperX, launches a new model today. Called "Alloy Elite 2," it is the successor to the wildly popular first-gen Alloy Elite. This time, you get "pudding" keycaps, which feature translucent sides for a brighter and more colorful RGB experience. Thankfully, the volume wheel and media buttons make a return.

Windows 10 May 2020 Update is breaking OneDrive Files On-Demand for some people
Microsoft has acknowledged OneDrive connectivity problems on some devices that have been upgraded to Windows 10 May 2020 Update (Windows 10 version 2004).
An error message reading "OneDrive cannot connect to Windows" informs affected users that Files On-Demand require an internet connection to function. The problem means that people are unable to access some of their files -- at least until they apply a workaround.

Lexar launches SL200 USB-C portable SSD
If you want to store your data externally, you can always go with a mechanical hard disk drive. That makes sense, as HDDs are typically a more cost effective option when compared to solid state drives. With that said, SSDs have dropped in price a lot lately, and are getting larger storage capacities all the time. For instance, both Sabrent and Samsung recently showed off 8TB SSDs. Not to mention, solid state drives are faster and have no moving parts, making them worth the premium for some consumers.
Lexar recently announced a new portable SSD that uses USB-C for connectivity, and it is rather affordable. Called "SL200," it appears to use a SATA drive internally, so it isn't the fastest option on the market. With that said, it is still significantly faster than a USB hard disk drive. Your PC doesn't have USB-C? Don't worry. The attractive drive comes with both a USB-C to USB-C cable and a USB-C to USB-A cable in the box.
