
Fedora Linux 39 launches with GNOME 45
Twenty years after the debut of Fedora Core 1, Fedora Project commemorates this milestone with the release of Fedora Linux 39 (available here). This iteration brings forward a suite of enhancements and updates that solidify its stance as a versatile operating system for a multitude of platforms. At the heart of Fedora Workstation 39 is GNOME 45, which promises not only improved performance but a slew of user experience refinements.
GNOME 45 introduces new widgets and a redesigned Image Viewer application, boosting both aesthetics and functionality. The desktop environment has become more informative with a dynamic workspace indicator, giving users a clear view of their virtual desktop landscape. A new camera activity indicator, alongside the pre-existing privacy features, now notifies users when their camera is accessed.

Organizations turn to GenAI to combat downtime
Downtime-producing incidents such as application outages and service degradation are putting organizations at risk of losing up to $499,999 per hour on average, so it's no surprise they're turning to AI to help their responses.
A new State of DevOps Automation and AI report from Transposit shows 84.5 percent of respondents either believe AI can significantly streamline their incident management processes and improve overall efficiency or are excited about the opportunities AI presents for automating certain aspects of incident management.

Unauthorized apps put businesses at risk
The risks from shadow and unauthorized apps have been known for years, but new research from Armis finds employees of 67 percent of UK organizations are introducing risk to the business by downloading applications and software onto assets without the knowledge or management of IT or security teams.
In addition the study, carried out by Vanson Bourne, finds 39 percent of enterprises admit to feeling challenged by increasingly complicated regulations and governance requirements.

Social media security issues pose threat to election campaigns
A new report from access management platform Cerby highlights the critical need for best practices for businesses and political leaders to secure their accounts as the November 2024 US elections quickly approach.
Researchers analyzed social media platforms Facebook, Twitter (X), Instagram, TikTok, and YouTube across six key security parameters. The report provides detailed insights into gaps in their support for enterprise-grade authentication and authorization.

Proton VPN rolls out new Linux app
Many people choose to browse the internet using a VPN because it offers a number of benefits including privacy and safety, and this is true whatever operating system you use.
With the launch of an all new app for Linux, Proton VPN is offering users of the open source OS greater functionality and a more intuitive interface. The Proton VPN Linux app natively supports Proton VPN's core security and privacy features.

HyperX launches Clutch Gladiate RGB Gaming Controller for Xbox and PC
HyperX has unveiled its latest product -- the Clutch Gladiate RGB Gaming Controller. This new wired controller is not just a treat for the eyes with its transparent design and customizable full-body RGB lighting but also a precision controller designed to enhance the gaming experience for Xbox users.
Sean Peralta, HyperX's Director of Product Management, emphasizes that the Clutch Gladiate RGB is "crafted to provide players with an immersive gaming experience and extensive customization options." Peralta adds that the controller is, "Designed to cater to every gamer's unique preferences and style, it gives gamers complete control and elevates their gameplay to new heights."

TCL's eye-friendly NXTPAPER 11 Android tablet now available for purchase
In an era where digital screens are as ubiquitous as the air we breathe, TCL Mobile is stepping up with a compelling proposition -- a tablet that's easy on the eyes without sacrificing performance. Enter the NXTPAPER 11, now hitting the digital shelves of TCL.com at a wallet-friendly $229.99.
TCL's NXTPAPER technology isn't just another incremental upgrade; it's a thoughtful response to our ever-increasing screen time. The NXTPAPER 11 tablet significantly cuts down harmful blue light exposure by up to 61 percent, a boon for the digital workforce and binge-watchers alike. With a matte finish and textured surface, this device ditches the glossy sheen of traditional tablets for an e-reader-like experience that's less taxing on the eyes.

IT pros worry about Kubernetes security
A new survey of 800 security and IT leaders from large organizations shows 76 percent of security and IT pros believe we are heading towards a cloud reckoning in terms of costs and security.
The study from Venafi finds that 84 percent believe Kubernetes will soon be the main platform used to develop all applications. But, three-quarters worry that the speed and complexity of Kubernetes and containers is creating new security blind spots.

Building an effective and insurable IoT security policy [Q&A]
As businesses look to manage their cybersecurity risk, many have turned to insurance to cover the financial implications of a successful breach.
However, insurers naturally want to limit their own exposure to risk and the small print of the policy may limit some claims. In particular this can apply to IoT devices which represent a major unprotected attack surface in corporate networks.
Get 'Sort Your Career Out: And Make More Money' (worth $14) for FREE
The best investment you can make is in yourself and your career.
Sort Your Career Out is your go-to guide for building a career that you love. Dream jobs don't just come along: you need to make them happen. And this is the book that will show you how, from creating the ultimate career strategy to getting paid what you're really worth. (Hint: It's not just about changing the font on your resume!)
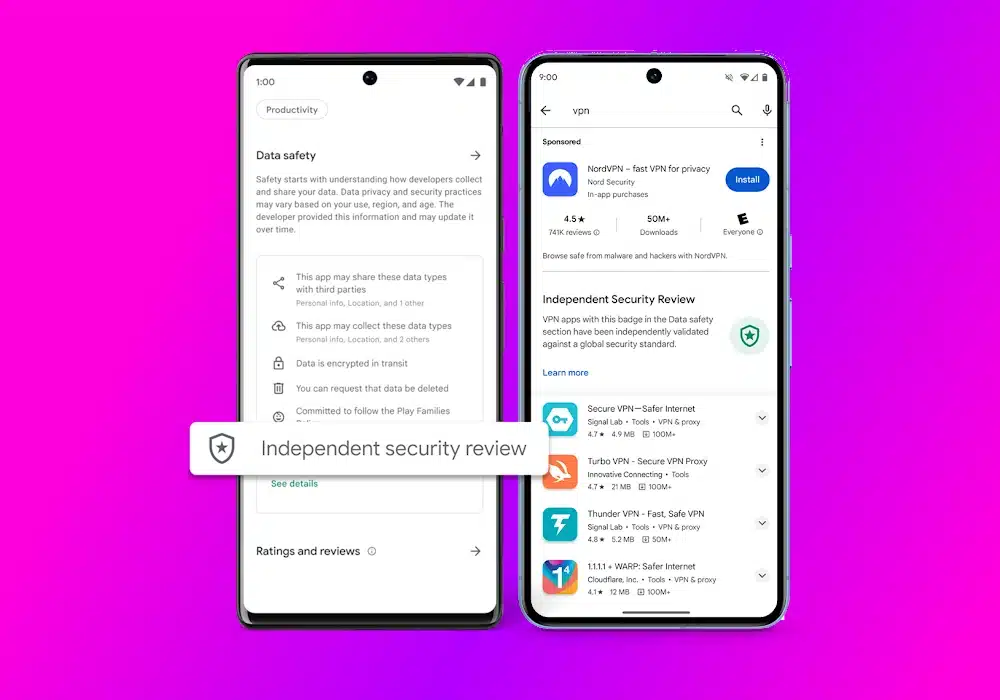
Google has a quixotic plan to make it easier to choose a safe and reliable VPN
If you're in the market for a VPN, you're not short of choice. In fact the sheer number of VPN apps out there can be quite overwhelming, and it's a situation that is hardly improved by the existence of a seemingly endless number of fake tools.
So Google has come up with something of a solution -- albeit one that is only going to be of help to Android users. The company is looking to make Google Play a safer place to inhabit, and as part of this it is going to be highlighting VPN apps that have been independently audited so users know they can be trusted. The likes of NordVPN, Express VPN and Google's own Google One are among the first to get the seal of approval.

Microsoft is killing off three Windows services because of security concerns
It is usually the case that new versions of Windows see the arrival of new features and options, but Microsoft is also known to take things away. This month, Microsoft has taken the decision to deprecate three features and services, including WebDAV, in Windows 10 and Windows 11.
Also for the chop are the Remote Mailslots protocol and the Computer Browser service. The reason for killing off the trio is security, with age meaning that there are now far better options available.
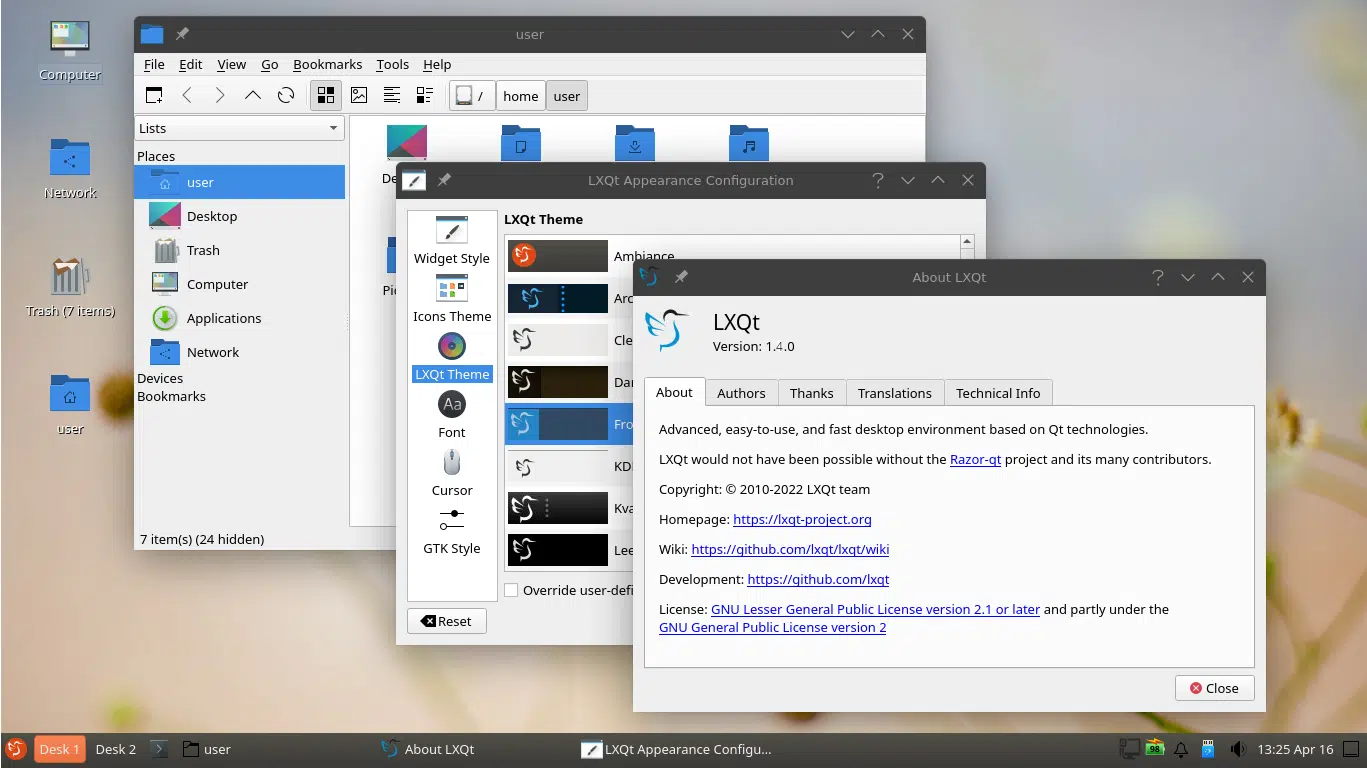
LXQt 1.4.0 lightweight Qt Linux desktop environment is here
The LXQt team has officially unveiled LXQt 1.4.0, marking a significant step forward for the “Lightweight Qt Desktop Environment.” This release underscores the team's commitment to providing a sleek yet powerful user interface.
At the heart of this release is the transition to Qt 5.15, the final Long-Term Support (LTS) version of Qt5. This change sets the foundation for the upcoming journey towards Qt6, with the LXQt team expressing a robust resolve to embrace Qt6 in the subsequent release, even if it necessitates a delay.
Three ways AI is changing the private equity game
Financial market participants, including banks, insurance companies, pension funds, and hedge funds, are all actively exploring ways to leverage artificial intelligence (AI), and private equity (PE) firms are no exception.
Three areas that are showing a significant return on investment (ROI) for AI among PE firms are deal flow, investment pre-screening, and risk intelligence, because it’s these areas where AI is helping them shift their window to act earlier than their peers. The private companies that PE firms invest in are simply far less transparent than public ones: There’s just not as much information about them, and the information that exists is generally much harder to get.

Three E-signature adoption trends that may surprise you
It’s well documented that the pandemic supercharged digital transformation speeds for countless organizations and disrupted how we work, live, and transact.
In the shift from ink to e-signatures across industries, I have witnessed three important yet somewhat under-the-radar adoption trends that support the recent IDC findings that 86 percent of IT decision-makers say that they have invested in e-signature software in the past year and 85 percent plan to do so in the next 12-18 months.


