The role of service mesh in application security [Q&A]
As organizations embrace cloud-native development, they are building new types of applications and microservices that are easier to scale and add more business value.
But the growing adoption of microservices has introduced new security risks because microservices and modern applications contain more 'pieces' that increase the attack surface.

Microsoft is changing the release schedule for Windows update previews
For the majority of Windows users, OS updates are just something that happens in the background. But for anyone who keeps a closer eye on things, the monthly Patch Tuesday is an important day when they know the latest "stable" versions of Windows updates are released.
For some time, however, Microsoft has released preview versions of updates ahead of the wider rollout, giving eager Windows users the chance to grab the latest fixes faster -- and also serve as beta testers. Now the company has announced that a new schedule for non-security preview releases is to be used from next month.

Windows 11 Snipping Tool has a serious privacy flaw that can expose information cropped out of screenshots
Microsoft Snipping Tool utility has been found to have a vulnerability that means that screenshots that have been cropped can be very easily uncropped, potentially exposing sensitive information.
The Snipping Tool is one of the most useful tools to be found in Windows 11, making it easy to take a variety of screenshots -- and, more recently, record screen activity -- without the need for third-party software. But the way in which the app crops images means that edited images are really just the original screengrab; 'cropped' parts are simply hidden and easily restored.

Canonical and NVIDIA work to make AI more accessible in the enterprise
In 2018, OpenAI reported that the amount of computing power used in large-scale AI training runs had been doubled every 3.4 months since 2012. Around the same time, the volume of data generated also increased dramatically.
This means traditional, general-purpose enterprise infrastructure can't deliver the required computing power, nor can it support the petabytes of data required to train accurate AI models at this scale. Instead, enterprises need dedicated hardware designed for AI workloads.

Delivering good search results is essential but hard to do
Whether you're trying to buy something or just looking for information, not being able to find what you want on a website is frustrating.
So it's not surprising that in a new survey of search practitioners from website search platform Lucidworks, 100 percent of respondents rank search relevance as being 'Highly Important'. What's more, 76 percent expect search relevance to become even more important in the future.

Only 15 percent of companies are ready for cyber threats
Just 15 percent of organizations globally have the 'Mature' level of readiness needed to be resilient against today's modern cybersecurity risks, according to Cisco's first-ever Cybersecurity Readiness Index.
More than half (55 percent) of companies globally fall into the Beginner (eight percent) or Formative (47 percent) stages, meaning they are performing below average on cybersecurity readiness.
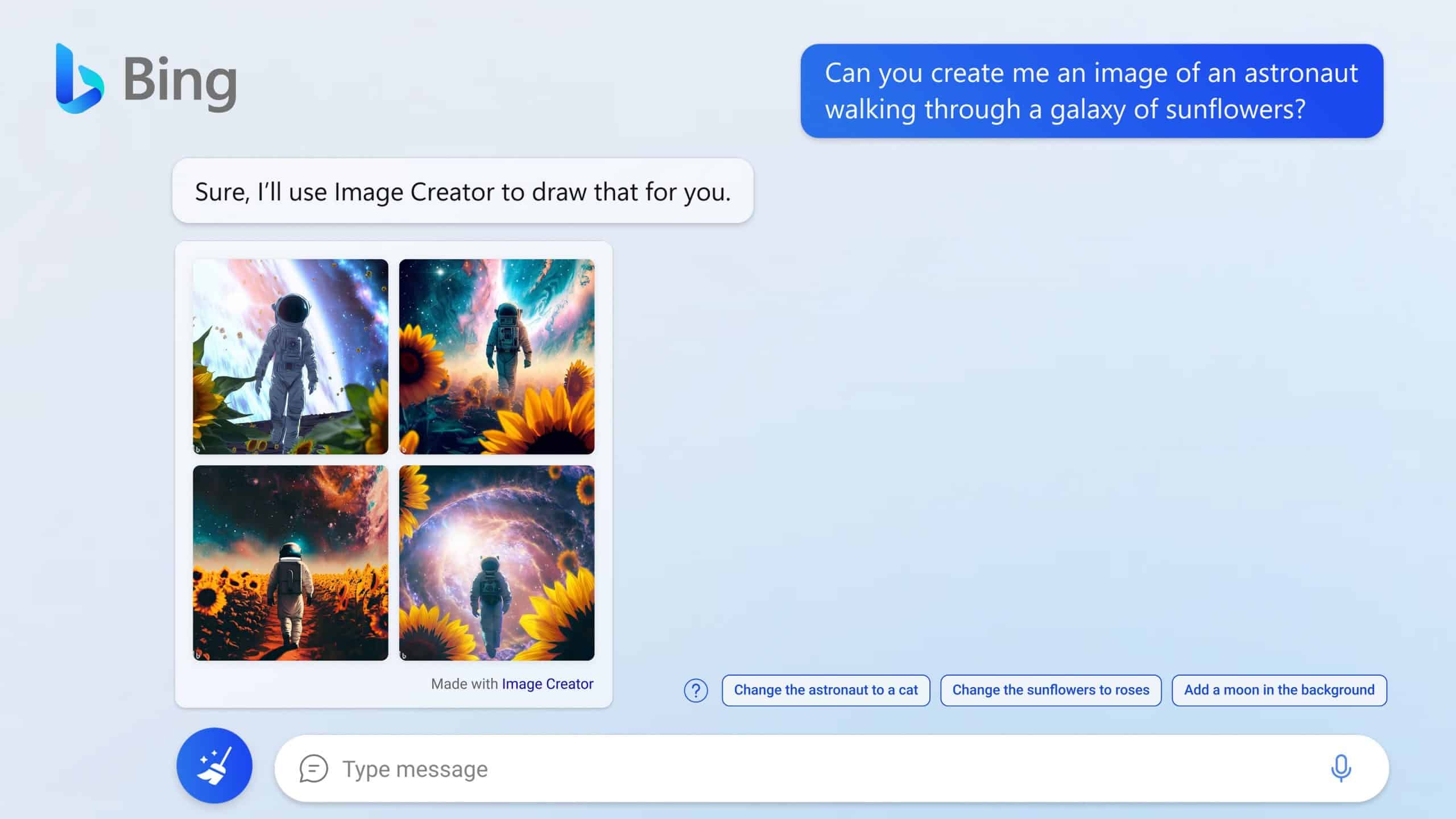
Microsoft launches DALL-E-based, AI-powered Bing Image Creator
Continuing its AI push, Microsoft has announced Bing Image Creator. Powered by OpenAI's DALL-E, the tool can be used to generate images using artificial intelligence.
Microsoft says that Bing Image Creator will form part of Bing chat, and it will accept natural language prompts to create (just about) any sort of image you might want. The tool will also be made available in Microsoft Edge, making it -- the company is quick to highlight -- the first and only browser with an integrated AI-powered image generator.

Ransomware surges as threat actors get more aggressive
Ransomware and extortion actors are utilizing more aggressive tactics to pressure organizations, with harassment being involved 20 times more often than in 2021, according to a new report.
The study, from Palo Alto Networks' Unit 42 threat intelligence team, finds harassment is typically carried out via phone calls and emails targeting a specific individual, often in the C-suite, to pressure them into paying a ransom demand.

Windows 11 Moment 2 update is slowing SSDs and putting system boot times in slo-mo
While there was much interest and excitement surrounding the release of the Moment 2 update for Windows 11, seasoned users were bracing themselves for the inevitable problems to emerge. And emerge they have.
There are a growing number of complaints from people who have installed the update that their system boot times have massively increased. There are also serious issues with severely reduced SSD performance, leading to slow file transfers and poor overall performance.
Kingston announces overclockable FURY Renegade Pro DDR5 Registered DIMMs
If your server, desktop, or workstation can use DDR5 Registered DIMMs, today is your lucky day. You see, popular memory-maker Kingston has announced impressive new Renegade Pro DDR5 RDIMMs under its "Fury" line.
What makes these sticks particularly impressive is they can be overclocked. Kingston will be offering the FURY Renegade Pro DDR5 RDIMM kits in various speeds (4800MT/s, 5600MT/s, and 6000MT/s) and capacities (16GB, 32GB, 64GB, 128GB, and 256GB).
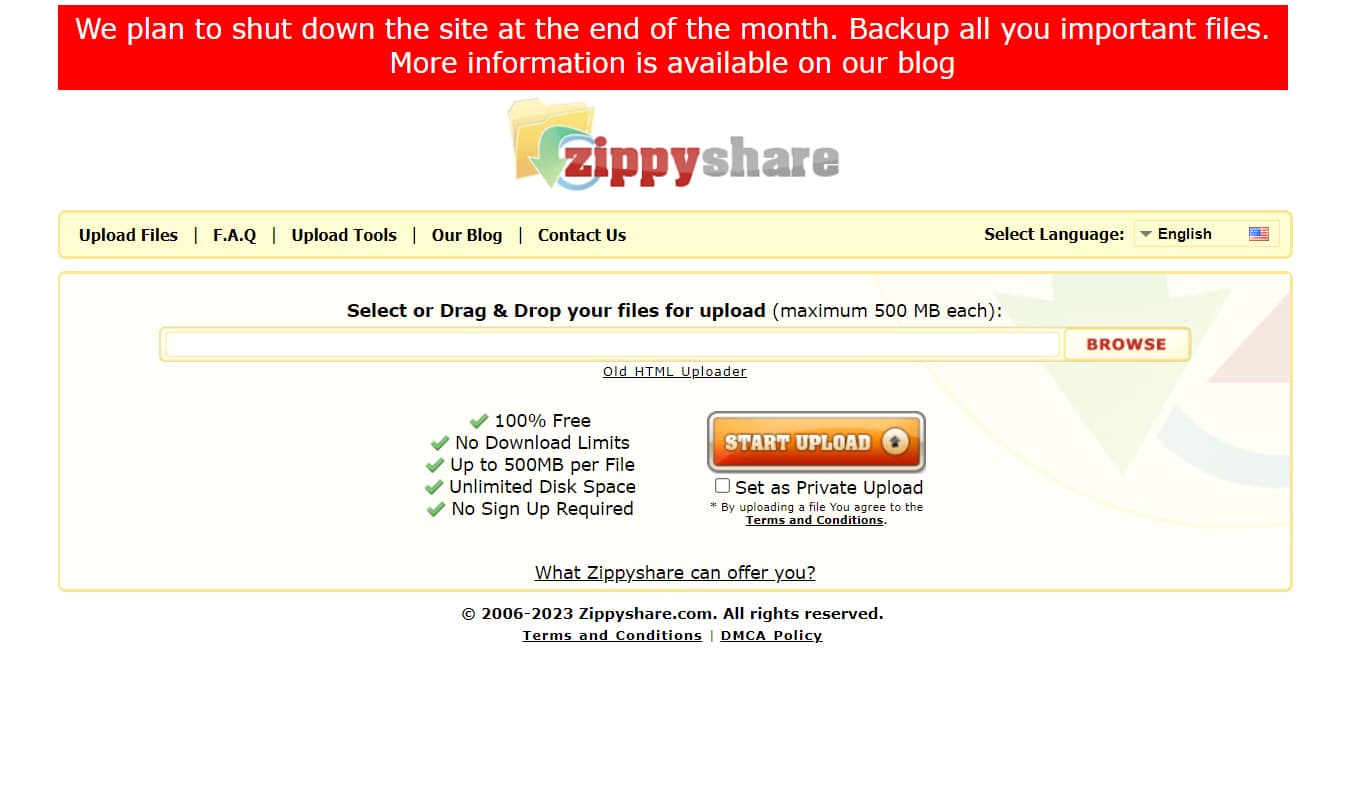
Veteran file hosting service Zippyshare to shut down at the end of the month
Although there are many file hosting services to choose from, Zippyshare is one of the better known, having been around since 2006.
Providing an easy, fuss-free way to store and share files, Zippyshare has a lot of fans, but it’s been struggling to make ends meet recently, despite still seeing around 45 million visits a month.

How to avoid fraud while remaining compliant
The financial technology (fintech) industry is a rapidly expanding web of innovation, but it is also becoming increasingly entangled by challenges posed by cybercriminals. These bad actors threaten both data security and regulatory compliance, which can result in heavy fines for noncompliance.
Such fines pose a significant risk for entrepreneurs seeking to quickly scale their operations, as they cannot afford to be bogged down by regulatory issues. Even established businesses find it challenging to navigate the complex layers of financial regulations, let alone startups.

ForgeRock launches password-free enterprise identity platform
People have been predicting the end of the password for a very long time, yet they still remain key to securing access to many systems.
Maybe the end is edging just a bit closer though as ForgeRock announces Enterprise Connect Passwordless, a new passwordless authentication solution that eliminates the need for users to interact with passwords inside large organizations.

Why a bigger budget isn't necessarily the key to good cybersecurity [Q&A]
Cyberattacks are expected to reach historic levels this year, in both volume and sophistication, yet many organizations are reducing their 2023 cybersecurity budgets.
We spoke to Steve Benton, VP of threat research at intelligence-driven cybersecurity specialist Anomali, to discover how a different approach might offer strong protection without breaking the bank.

Microsoft tests option to let you receive Windows 11 updates sooner
Microsoft is working on a new option for Windows 11 that will give users the ability to receive updates for the operating system faster. With the option enabled, there will be no need to wait until Patch Tuesday each month in order to get the latest bug fixes, or even new features.
It also means that there will be no need to manually hunt down the preview versions of updates Microsoft makes available. If this sounds interesting, it is possible to get on board and try out the early access feature right now.