
GCHQ arrives on Twitter to give a more public face to the spy agency
The UK's GCHQ -- like its US counterpart the NSA -- is an agency traditionally shrouded in secrecy. Tasked with the job of spying on all and sundry in the name of intelligence gathering, the agency has just joined Twitter, greeting other users with an unoriginal "Hello, world".
With the concerns about privacy and security that blew up in the wake of Edward Snowden's NSA surveillance revelation, spy agencies around the world have been on a mission to boost their public image. GCHQ -- complete with the blue tick reserved for verified accounts -- will use Twitter to "provide news, updates, and opinions".
Belgian police warn that Facebook Reactions pose a serious privacy risk
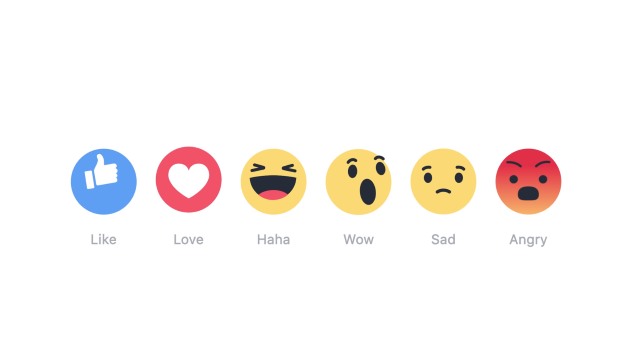
Police in Belgium are warning people not to use Facebook Reactions because of the risk they pose to privacy. Introduced recently to supplement the iconic Like option, Reactions give Facebook users the chance to respond to content with Love, Haha, Wow, Sad, and Angry emoji.
But Belgian police have issued a 'Safe Browsing' warning advising that Facebook is using Reactions to gather information about social network users. Specifically, the police warn that in using Reactions to express emotions, users are giving Facebook the opportunity to build up a more detailed personal profile about them and use that information to deliver closely targeted advertising.

Facebook panders to European privacy concerns by stripping facial recognition from Moments app
Facebook has rolled out its photo-sharing app Moments around the world, and users in Europe have been treated to a modified version. Specifically, the European version of the app lacks the facial recognition feature that allows for automatic tagging of people.
In many ways, Facebook has been forced to release a degraded version of Moments to its EU audience because of the varying privacy laws that exist in different countries. The hobbled app will not attempt to identify individuals in photos, but will group together images that "appear to include the same face".

Microsoft Edge users can now install Adblock Plus or AdBlock extensions
Extensions, or the lack thereof, have been stumbling block for many would-be Microsoft Edge users. Support for add-ons has finally arrived, bringing with it the potential for something people have been asking for since Edge first appeared -- the ability to block ads.
It had previously been thought that Edge might feature native ad blocking, but this turned out to be a matter of poor communication from Microsoft. We've already shown you a slightly bodged-together way of blocking ads in Edge, but now Adblock Plus and AdBlock extensions have been officially released to the Windows Store.

EU GDPR: Get your data privacy act together
The moment of reckoning is on its way for companies that collect or store data on European Union citizens. Last week EU legislators signed data privacy regulations into law, creating what may be the most stringent data protection law in place today. The requirements will not be easy for many companies to meet and will demand financial and personnel resources. There is sure to be criticism that the EU stifles technology innovation. In reality, the GDPR demonstrates a progressive approach to data transactions and the digital economy. The introduction of the regulation states, "The protection of natural persons in relation to the processing of personal data is a fundamental right…".
Essentially, the law codifies the concept that data transactions come with responsibility on the part of the collector. As technology continues to advance, establishing this foundation of trust is a necessary step. Complying with the regulation may seem onerous, but think from the consumer’s perspective. Organizations gather more data than ever. Huge headaches and hardships arise when data is stolen or lost. The regulation puts in place best practices to ensure companies offer a necessary level of security and treat personal data with the respect it deserves.

Think Privacy CEO launches site to name publishers who illegally detect and circumvent adblockers
Adblockers are, have been, and will continue to be a matter of some controversy. While sites rely on ad income to stay afloat, users are understandably irked by a barrage of flashy commercials and are increasingly turning to adblocking. To fight back, some sites are using various methods to detect the presence of an adblocker and then bypassing it.
This, in turn, upsets people once again, and the CEO of privacy and security consortium Think Privacy, Alexander Hanff, has come up with a solution. To fight back he has set up a website that names and shames those sites that "use illegal methods to detect that you are using an adblocker".

Facebook Messenger to gain privacy-enhancing self-destructing messages
With the ongoing debate about privacy and encryption, the rollout of end-to-end encryption to Facebook-owned WhatsApp came as little surprise. Now Facebook Messenger is set to gain a couple of privacy-enhancing features including self-destructing messages.
Already found in other messaging tools such as SnapChat and Telegram, self-destructing messages have been unearthed in Messenger for iOS version 68.0. As you would expect, the feature makes it possible to place a time limit on how long messages are visible for, making it ideal for communicating sensitive information.

Facebook transparency report shows increase in government data requests, most with gagging orders
Facebook has published its latest Global Government Requests Report covering the second half of 2015. The transparency report reveals that there has been as 13 percent increase in the number of government requests for data, but it also shows that Facebook is still not able to be as transparent as it might want.
For the first time the social network is able to report about the number of data requests that have a non-disclosure order attached to them. More than half of the requests -- 60 percent, in fact -- have gagging orders that prevent Facebook from notifying users about requests for their data.

Waze vulnerability allows hackers to track you
Users of Google’s navigation app Waze seem to be at risk of being followed, as a vulnerability in the app could allow hackers to stalk the users of the app in real-time, a group of researchers from the University of California has found.
The researchers reverse-engineered Waze’s server code and discovered that thousands of "ghost drivers" could be created on Waze’s systems, which can monitor the real drivers around them. Hackers could even create virtual traffic jams, an exploit to track Waze users in real-time.

Human rights group Liberty rips into Snooper's Charter with video highlighting privacy issues
The Snooper's Charter -- or the Investigatory Powers Bill -- is a highly controversial piece of legislation the UK government is trying to bring into force to allow for the bulk collection of data, NSA-style. Outside of government, it is widely regarded as a massive invasion of privacy, and the human rights group Liberty is just one of the organizations that is very vocally opposed to it.
The bill will require ISPs to record customers' browsing histories for an entire year, and will permit the government to remotely hack phones and computers, as well as requiring tech companies to provide backdoor access to encrypted data. To highlight what is at stake, Liberty is running a No #SnoopersCharter campaign, and has released a video that attacks the notion of 'if you have nothing to hide, you have nothing to fear' head on.

BlackBerry Priv gets Android 6.0 Marshmallow
Android 6.0 launched over half a year ago, but even today there are still lots of devices that have yet to receive the software upgrade to Marshmallow. In fact, at the beginning of this month fewer than one in 20 were running Google's latest mobile operating system.
For BlackBerry Priv users though things are looking up. The Canadian maker has announced the Marshmallow rollout for its first Android smartphone, introducing improvements to the camera, battery, privacy, security, and more.

Twitter makes it easier to report abusive tweets en masse
There has been a lot of interest in online abuse in recent months, and social networks are taking steps to weed out the trolls and abusers. Twitter has already introduced a number of measures to help tackle trolls, and today announces the availability of a new reporting tool for users.
Now rather than having to report a number of abusive tweets individually, it is possible to report up to five tweets simultaneously. As well as reducing the workload for someone who feels the need to report content, the new tool also makes things easier for Twitter as it allows for additional information to be gathered.

US Justice Department accesses another iPhone without Apple’s help
When it came to the San Bernardino iPhone, Apple was ready to dig in its heels and refuse to help the FBI to gain access to the encrypted contents. As it turns out, the company needn’t have bothered shouting as a third party helped instead. Now the same thing has happened with another iPhone.
This time around, the Justice Department had been looking for help accessing an iPhone at the center of a drugs case in New York. But now federal prosecutors have said they no longer need Apple’s help as they have managed to get by the lockscreen.

Nearly half of EU businesses don't know where their data's located
According to a survey by the cloud hosting firm UKFast, nearly half of businesses are clueless as to where their data is located.
To come to its findings, the company surveyed over 300 IT decision makers in EU businesses, with 47 percent of them unaware of where their personal and company data was hosted.

With security and privacy in mind, will more browsers follow Opera's lead and offer free VPN?
The modern internet user is somewhat paradoxical -- looking to be more connected and contactable than ever before, whilst simultaneously seeking privacy. Can the two ideas live side by side? It's a tricky balancing act, but many people turn to VPN tools to increase their security and privacy online.
Opera is the first web browser to bundle a free VPN tool as standard (with unlimited VPN data, no less), and it's hard to imagine that the competition won’t follow suit. Nothing has yet been announced, but the appearance of versions of Chrome or Firefox with integrated VPN would hardly be a surprise -- or would it? And how would you feel about a VPN tool supplied by Google?
